Design, Fit And Maintain
Posted on 04-10-2020 03:47 PM

On This Page
- Critical Components of Access Control Design
- The ABCs of Access Control and Which is Better for Cloud Services?
- Field Guide to Access Control: 20 Questions about Access Control
- UW-Madison - IT - Access Control Services Standard
- Types of access control systems we offer:
- Access Control – Frequently Asked Questions
Critical Components of Access Control Design
We have the experience to select the right access control systems and design systems that operate effectively and efficiently within your existing building infrastructure. Access control systems greatly help to prevent time theft from employees. If an employee isn’t on the schedule or on site, they won’t be able to get in. Access control is also critical to the prevention of unauthorized access to your property and valued assets. 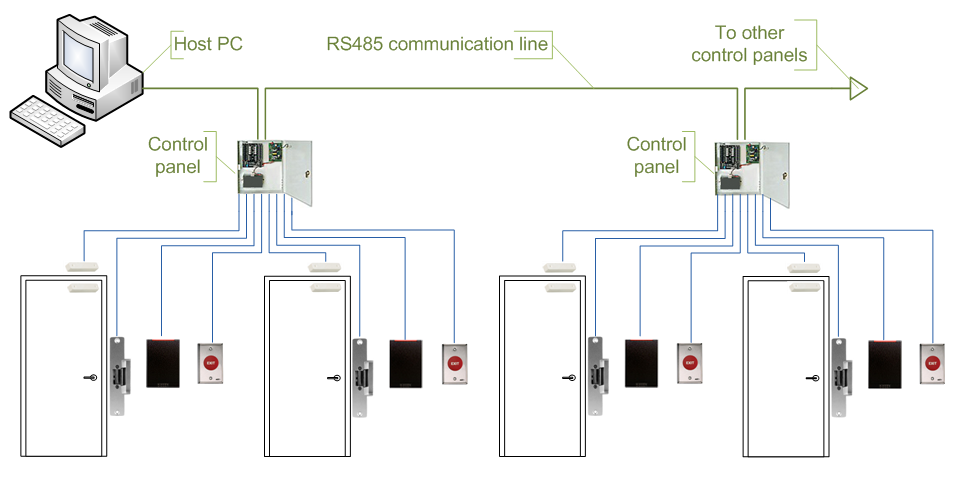 Choosing the right security contractor to provide access control for your business is equally critical.
Choosing the right security contractor to provide access control for your business is equally critical.
Secure area access to people with a designated need. Program common areas for unlimited access. Update effortlessly as circumstances change. Manage security from one location link multiple facility systems to a central server so that you can monitor access points and manage user databases from one location. You can even manage your access control system through a web portal. Read more about access control here.
A construction site access control system is designed to manage the access of authorized personnel on large job sites. Combining rfid technology components such as biometric readers and electronic turnstiles, an automated way of providing access to fenced construction zones is made possible. Made knowing construction workers have their hands full with tools and materials, the access control system can be configured to be completely hands-free, enabling convenient and efficient access to any area on the site.
The ABCs of Access Control and Which is Better for Cloud Services?
According to okta’s business at work 2019 report , nearly 40% of employees use the same two to four passwords to access over 100 apps on average. In the workplace, this means corporate it administrators have their hands full managing user credentials for multiple systems. As organizations embrace cloud-based tools for a mix of on-prem and online services, it admins have become responsible for securing access to many platforms with varying identity management and access control solutions. This can be challenging for it teams, and can also lead to a frustrated user base that needs to stay on top of multiple logins.
Access control service, or windows azure access control service (acs) is a microsoft -owned cloud-based service that provides an easy way of authenticating and authorizing users to gain access to web applications and services while allowing the features of authentication and authorization to be factored out of the application code. This facilitates application development while at the same time providing users the benefit of being able to log into multiple applications with a reduced number of authentications, and in some cases only one authentication. The system provides an authorization store that can be accessed programmatically as well as via a management portal. Once authorizations are configured, a user coming to an application via acs arrives at the application entrance with not only an authentication token, but also a set of authorization claims attached to the token. Acs was retired by microsoft on november 7, 2018.
Most business systems are already cloud based. Your chat messenger, email services, sales crm tool, marketing tools, and engineering productivity tools all sit on cloud servers. So why is your access control system still running on an on-premise laptop or server designed in 2002?.
It enables you to create and manage permissions for google cloud resources. It unifies access control for google cloud services into a single system and presents a consistent set of operations. For an overview of concepts, read iam overview.
Keeping in view the advancement in cloud computations, ip door access control platforms are now available in cloud. The services that are provided by the host include installation, administration, and management of isonas hardware. The cloud facilitates you to control and manage unlimited number of doors and access points situated in various areas on your mobile device. Learn more ….
Field Guide to Access Control: 20 Questions about Access Control
When investing in security for your business it is of the utmost importance that you know exactly what you are getting and that what you are investing in is right for your business and its needs. Access control is one of the most reliable and cost-effective forms of security but buying door entry systems is not the easiest task as there are so many options available on the market. It is important to ask a lot of questions when it comes to making this investment as you want to get peace of mind that you have made the right decision. If you are not an expert when it comes to access control and door entry systems in london then it is not always easy to know the type of questions that you need to ask yourself. With this in mind we have prepared a short guide that will inform you of the types of question that you should ask when you are looking to invest in door entry systems.
Our staff access control has become increasingly important for organizations of all shapes and sizes. Whether you are managing thousands of people on a college campus or a dozen employees in a local office, you must ensure their safety while on your property. Access control security (identity and visitor management) is a constant balancing act between convenience and security. If you have been asked to find and deploy an access control solution for your organization, you probably have a number of questions. How can you ensure safety while also supporting convenience? our editors have worked with technology integrators and it pros just like you to develop our new guide “rfp template: access control”.
IT - Access Control Services Standard
Microsoft azure access control service (acs) is a cloud service that provides user authentication and authorization for web applications and services. By using acs, you do not have to factor authentication and authorization into your application code. Instead of implementing an authentication system with user accounts that are specific to your application, you can let acs orchestrate the authentication and much of the authorization of your users. Acs integrates with standards-based identity providers, including enterprise directories such as active directory, and web identities such as microsoft account, google, yahoo!, and facebook.
We make security a priority. We are committed to providing our customers with the resources necessary to keep our facilities secure. Physical access control system (pacs): homeland security presidential directive 12 (hspd-12) expertise in migrating and implementing hspd-12 federal information processing standard (fips) compliant systems design services on full security integration and interoperability scope development and project management/oversight full understanding of gsa/federal acquisition services (fas) schedules and approved products list for fips.
Types of access control systems we offer:
If your facility is looking for ways to upgrade building security or is hoping to move on from a troublesome key entry system, access control systems are a robust solution. Offering simple management that is flexible and scaleable, access control systems enable you to provide the right access to the right people and to the right areas of your facility, at any time. Here are just a few key benefits that access control systems can provide to your facility’s comprehensive security system :.
Whatever your need and budget is, we can provide the equipment you need. There are no limits on the number of door readers that can be used with our systems and we can integrate over 100,000 cards to them. Some of the types of access control we install are:.
Access Control – Frequently Asked Questions
Our cloud access control makes it easier than ever to manage your gate access and activity. Below is a list of frequently asked questions about our cloud access control system. 1. Can i automatically assign gate codes? - yes, our system allows you to automatically assign a random code, or a code that is based off of their telephone number. 2. How do i let my customer know what their access code is?.
Managing employee and visitor access rights at single or multiple locations can become a complex task with many moving parts. But with safety and security on the line, you can’t afford to have a weak link or any gaps in your system. But how can you ensure that you meet your security targets while also achieving the flexibility to deal with new locations, new requirements and new technology? touchstar’s lynden jones reviews some of the most frequently asked questions to provide an overview of how access control works and how touchstar’s end-to-end management service can help users implement the right solution.
Access Control Components
There are a number of componants within an access control system such as to control a door you need a ‘door controller’ which will be connected to an electricity supply. The door controller communicates with the locking device and in large systems will communicate with the access control software to record who, when and location the door open/closed.
Outside there will be a keypad or a card/fob/fingerprint/face reader. To people without access rights the door is securely locked. To people with access rights the door will open and may (in software controlled systems) record the time and date they accessed the building.
On larger, software controlled systems, the door controllers are linked together by cable or wirelessly to the managers computer. At the computer the software will be recording the door operations and laying down a reviewable audit. The manager will have records of registered users. The manager has rights to add users, remove users or further control users by the addition of time windows. Identity cards can be made with photos of the users and personal information records can be kept under GPDR rules.